Instalando Graylog 2 no Debian 8
Nesse post veremos a instalação do Graylog 2. Mas o que é isso?! De forma resumida ele centraliza e armazena os logs da sua infraestrutura, possibilitando uma análise aprofundada, alarmes, notificações, histórico, gráficos e etc… isso tudo facilitando a sua vida ;)
Vamos começar a instalação, o ambiente utilizado foi:
|
1 2 3 4 5 |
SO: Debian GNU/Linux 8 Kernel: Linux debian 3.16.0-4-amd64 Graylog 2.2 MongoDB Elasticsearh 2.x |
Começamos adicionado repositório Backports do Debian, atualizando e fazendo upgrade em seguida reinicie o sistema.:
|
1 2 3 |
santos@graylog-BTI:~$ sudo echo "deb http://ftp.debian.org/debian jessie-backports main" > /etc/apt/sources.list.d/backports.list santos@graylog-BTI:~$ sudo apt-get update && sudo apt-get upgrade santos@graylog-BTI:~$ sudo reboot |
E instalamos alguns pré-requisitos adicionais:
|
1 |
santos@graylog-BTI:~$ sudo apt-get install apt-transport-https uuid-runtime pwgen curl |
O Graylog também faz uso do Java Headless, usamos o Backport:
|
1 |
santos@graylog-BTI:~$ sudo apt install -t jessie-backports openjdk-8-jre-headless ca-certificates-java |
Para o Graylog armazenar os logs, iremos instalar o MongoDB, para isso faça:
|
1 |
santos@graylog-BTI:~$ sudo apt-get install mongodb-server |
Instalaremos agora o Elastisearch, o Graylog na versão 2.x requer o Elastichsearch na versão 2.x para funcionar. Veja:
|
1 2 3 4 |
santos@graylog-BTI:/opt$ wget -qO - https://packages.elastic.co/GPG-KEY-elasticsearch | sudo apt-key add - santos@graylog-BTI:/opt$ echo "deb https://packages.elastic.co/elasticsearch/2.x/debian stable main" | sudo tee -a /etc/apt/sources.list.d/elasticsearch-2.x.list deb santos@graylog-BTI:/opt$ sudo apt-get update && sudo apt-get install elasticsearch |
Finalizado a instalação do Elastisearch, vamos configura-lo:
|
1 |
root@graylog-BTI:/opt# nano /etc/elasticsearch/elasticsearch.yml |
Altere o seguinte parâmetro:
|
1 |
cluster.name: graylog |
Após a instalação, vamos recarregar as configurações, habilitar o serviço e iniciar o Elasticsearch:
|
1 2 3 |
santos@graylog-BTI:/opt# sudo systemctl daemon-reload santos@graylog-BTI:/opt# sudo systemctl enable elasticsearch.service santos@graylog-BTI:/opt# sudo systemctl restart elasticsearch.service |
Agora faremos a instalação, configuração do Graylog 2:
|
1 2 3 |
santos@graylog-BTI:/opt$ sudo wget https://packages.graylog2.org/repo/packages/graylog-2.2-repository_latest.deb santos@graylog-BTI:/opt$ sudo dpkg -i graylog-2.2-repository_latest.deb santos@graylog-BTI:/opt$ sudo apt-get update && sudo apt-get install graylog-server |
Antes de iniciar o Graylog precisamos gerar duas senhas: Uma para o password_secret e outra para root_password_sha2, então rodaremos o seguinte comando
|
1 |
echo -n yourpassword | sha256sum |
Como exemplo usaremos a senha boteco para password_secret e admin para root_password_sha2, que fica dessa forma:
|
1 2 3 4 |
root@graylog-BTI:/opt# echo -n boteco | sha256sum f014ac9276709828f0265a799a7642b4399a9d4686ad65fcd8b10741cce97827 root@graylog-BTI:/opt# echo -n admin | sha256sum 8c6976e5b5410415bde908bd4dee15dfb167a9c873fc4bb8a81f6f2ab448a918 |
Agora iremos copiar o hash gerado e iremos editar o arquivo de configuração /etc/graylog/server/server.conf. Vou reforçar aqui que essas senhas mostradas NÃO devem ser usadas em ambiente de produção, escolham senhas mais robustas!
Altere agora os seguintes parâmetros:
|
1 2 3 4 5 |
password_secret =f014ac9276709828f0265a799a7642b4399a9d4686ad65fcd8b10741cce97827 root_password_sha2 =8c6976e5b5410415bde908bd4dee15dfb167a9c873fc4bb8a81f6f2ab448a918 rest_listen_uri = http://192.168.0.11.:9000/api/ web_listen_uri = http://192.168.0.11:9000/ rest_transport_uri = http://192.168.0.11:9000/api/ |
Observação: O IP informado acima é da minha VM, portanto rode o comando ifconfig para verificar qual seu IP e não deixe com endereço localhost 127.0.0.1.
Recarregue as configurações, habilite e inicie o serviço:
|
1 2 3 |
santos@graylog-BTI:~$ sudo systemctl daemon-reload santos@graylog-BTI:~$ sudo systemctl enable graylog-server.service santos@graylog-BTI:~$ sudo systemctl start graylog-server.service |
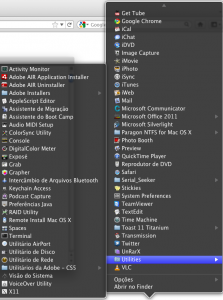
Pronto! Agora basta acessar em seu navegador http:<IP-Graylog:9000> e terá essa tela:

Acesse usando o usuário padrão admin e a senha que criamos anteriormente admin e verá a tela de boas vindas:

Com isso finalizamos a instalação do Graylog 2, nos próximos post faremos algumas configurações no próprio servidor e também em hosts linux e windows para enviarem seus logs ao Graylog 2. Até mais ;)
Referências:
http://docs.graylog.org/en/2.2/pages/installation/os/debian.html#
https://packages.debian.org/jessie/java-runtime-headless